Schedule of DNSSEC Activities at ICANN 56 in Helsinki
Posted by Dan York in DNSSEC, ICANN DNSSEC Workshops on June 25, 2016
 Starting on Monday, 27 June 2016, the ICANN 56 meeting will take place in Helsinki, Finland.
Starting on Monday, 27 June 2016, the ICANN 56 meeting will take place in Helsinki, Finland.
This is the first meeting in ICANN’s new shorter “B” format of a “policy forum”. As a result, there have been some changes to the schedule of DNSSEC activities (which are expected to return to their regular format for ICANN 57 this fall in Hyderabad):
- There is no “DNSSEC for Everyone” beginner session.
- The “DNSSEC Workshop” has moved from Wednesday to Monday and is only 4 hours instead of the usual 6+ hours.
- The “DNSSEC Implementers Gathering” has changed from Monday night to Tuesday night so as not to conflict with the ICANN reception.
Here is what the schedule looks like:
DNSSEC Workshop
The DNSSEC Workshop will take place on the morning of Monday, 27 June 2016. All times are Eastern European Summer Time (EEST), which is UTC+3.
We are grateful to four companies for their sponsorship of this event: Afilias, CIRA, Dyn and SIDN.
- 09:15-09:30–Introduction/Maps: Dan York, Internet Society
- 09:30-10:00–Measurement Survey of Server-Side DNSSEC Adoption: Matthäus Wander
- 10:00-10:15–Observation of DNSSEC Trends: Geoff Huston, APNIC
- 10:15-11:15–Panel Discussion: DNSSEC Deployment Challenges: Nick Shorey, Dani Grant, CloudFlare, Ari-Matti Husa, FICORA, Geoff Huston, APNIC
- 11:15-11:45–KSK Rollover and ZSK Length Increase: Roy Arends, ICANN and Duane Wessels, Verisign
- 11:45-12:00–DNSSEC Encryption Algorithms: Dan York, Internet Society, and Ondrej Sury, CZNIC
- 12:00-12:15–DNSSEC: How Can I Help? Dan York, Internet Society, and Russ Mundy, Parsons
- 12:15-12:30–DNSSEC/DNS Quiz: Roy Arends, ICANN
- 12:30-13:30–Sponsored Lunch
All sessions will be available for remote participation and will be recorded for later viewing:
- Adobe Connect https://icann.adobeconnect.com/hel56-veranda2
- English Audio http://stream.icann.org:8000/hel56-veranda2
- English Audio (Low Bitrate) http://stream.icann.org:8000/hel56-veranda2-en-lo.m3u
We’ve got some great sessions and we’re looking forward to another exciting session! And after lunch you can stay around for “Tech Day” where there will be a range of other DNS-related talks.
DNSSEC Implementers Gathering
On Tuesday evening, many of us who have been involved with DNSSEC, DANE or “DNS security” will gather informally at a local restaurant in Helsinki. We’ll have some light food, drinks and conversation. If you’d like to join us, please email Dan York at [email protected] .
And… that will be it! If you are at ICANN 56 please do say hello – you can find Dan York in these sessions… or drop him a note at [email protected] and he can arrange a time to connect.
Call for Participation – DNSSEC Workshop at ICANN 56 in Helsinki, Finland on 27 June 2016
Posted by Dan York in ICANN DNSSEC Workshops on April 28, 2016
 The DNSSEC Deployment Initiative and the Internet Society Deploy360 Programme, in cooperation with the ICANN Security and Stability Advisory Committee (SSAC), are planning a DNSSEC Workshop at the ICANN 56 meeting on 27 June 2016 in Helsinki, Finland. The DNSSEC Workshop has been a part of ICANN meetings for several years and has provided a forum for both experienced and new people to meet, present and discuss current and future DNSSEC deployments. For reference, the most recent session was held at the ICANN 55 meeting in Marrakech, Morocco, on 09 March 2016. The presentations and transcripts are available at: https://meetings.icann.org/en/marrakech55/schedule/wed-dnssec.
The DNSSEC Deployment Initiative and the Internet Society Deploy360 Programme, in cooperation with the ICANN Security and Stability Advisory Committee (SSAC), are planning a DNSSEC Workshop at the ICANN 56 meeting on 27 June 2016 in Helsinki, Finland. The DNSSEC Workshop has been a part of ICANN meetings for several years and has provided a forum for both experienced and new people to meet, present and discuss current and future DNSSEC deployments. For reference, the most recent session was held at the ICANN 55 meeting in Marrakech, Morocco, on 09 March 2016. The presentations and transcripts are available at: https://meetings.icann.org/en/marrakech55/schedule/wed-dnssec.
Examples of the types of topics we are seeking include:
1. DNSSEC Deployment Challenges
The program committee is seeking input from those that are interested in implementation of DNSSEC but have general or particular concerns with DNSSEC. In particular, we are seeking input from individuals that would be willing to participate in a panel that would discuss questions of the nature:
— What are your most significant concerns with DNSSEC, e.g., implementation, operation or something else?
— What do you expect DNSSEC to do for you and what doesn’t it do?
— What do you see as the most important trade-offs with respect to doing or not doing DNSSEC?
We are interested in presentations related to any aspect of DNSSEC such as zone signing, DNS response validation, applications use of DNSSEC, registry/registrar DNSSEC activities, etc.
2. DNSSEC by Default
As more and more applications and systems are available with DNSSEC enabled by default, the vast majority of today’s applications support DNSSEC but are not DNSSEC enabled by default. Are we ready to enable DNSSEC by default in all applications and services? We are interested in presentations by implementors on the reasoning that led to enable DNSSEC by default in their product or service. We are also interested in understanding those that elected not to enable DNSSEC by default and why, and what their plans are.
3. DNSSEC Encryption Algorithms
How do we make DNSSEC even more secure through the use of elliptic curve cryptography? What are the advantages of algorithms based on elliptic curves? And what steps need to happen to make this a reality? What challenges lie in the way? Over the past few months there have been discussions within the DNSSEC community about how we start down the path toward adding support for new cryptographic algorithms such as Ed25519 and Ed448. At ICANN 55 in Marrakech we had a panel session that explored why elliptic curve cryptography was interesting and some high level views on what needs to happen. At ICANN 56 we are interested in presentations that dive into greater detail about what needs to be done and how we start the process. More background information can be found in this document: https://datatracker.ietf.org/doc/draft-york-dnsop-deploying-dnssec-crypto-algs/
In addition, we welcome suggestions for additional topics.
If you are interested in participating, please send a brief (1-2 sentence) description of your proposed presentation to [email protected] by Wednesday, 18 May 2016.
We hope that you can join us.
Thank you,
Julie Hedlund
On behalf of the DNSSEC Workshop Program Committee:
Mark Elkins, DNS/ZACR
Cath Goulding, Nominet UK
Jean Robert Hountomey, AfricaCERT
Jacques Latour, .CA
Xiaodong Lee, CNNIC
Luciano Minuchin, NIC.AR
Russ Mundy, Parsons
Ondřej Surý, CZ.NIC
Yoshiro Yoneya, JPRS
Dan York, Internet Society
Next Monthly DNSSEC Coordination Call On March 24, 2016
For those who participate in the monthly “DNSSEC Coordination” calls where we discuss activities around accelerating the deployment of DNSSEC, there will NOT be a call tomorrow, March 3, as there would normally be (the first Thursday of the month).
On our last call in February we noted that:
- on March 3rd, many of us will be in transit to Marrakech for ICANN 55; and
- on April 7th, many of us will be in Buenos Aires for IETF 95.
We therefore decided to:
- Cancel the monthly call on March 3.
- Cancel the monthly call on April 7.
- Hold instead a call on Thursday, March 24, at the usual time of 11:00 US Eastern which will be 15:00 UTC.
Details for the conference call will be sent out as we get closer to March 24.
Note: if you would like to participate in these monthly calls, please join the dnssec-coord mailing list. All who want to accelerate the deployment of DNSSEC and DANE are welcome to join.
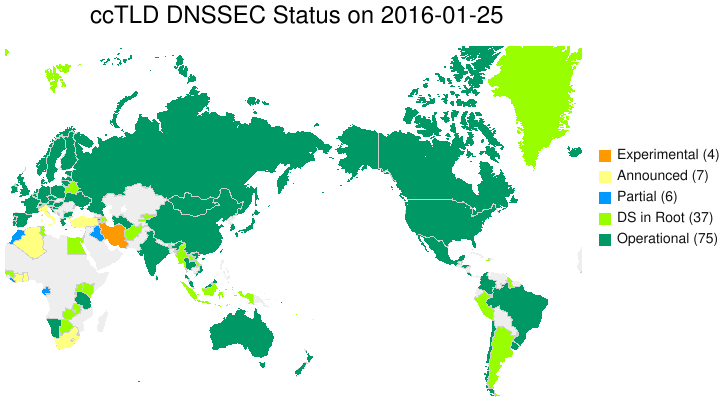
Updated DNSSEC Deployment Maps Available on Deploy360
Posted by Dan York in DNSSEC Deployment Maps on January 27, 2016
Today I’ve updated the page showing DNSSEC Deployment Maps over on the Deploy360 site. The maps are generated each Monday and sent to a mailing list (to which you can subscribe) and the latest versions are always available in the mailing list archives. However, from time to time I update the page to show the latest maps so that people can easily find them.
By the way, the latest ccTLD to sign with DNSSEC was Azerbaijan’s .AZ domain!
Call for Participation — ICANN DNSSEC Workshop at ICANN 55 in Marrakech, Morocco
Posted by Dan York in DNSSEC, ICANN DNSSEC Workshops on November 30, 2015
 The DNSSEC Deployment Initiative and the Internet Society Deploy360 Programme, in cooperation with the ICANN Security and Stability Advisory Committee (SSAC), are planning a DNSSEC Workshop at the ICANN 55 meeting on 09 March 2016 in Marrakech, Morocco. The DNSSEC Workshop has been a part of ICANN meetings for several years and has provided a forum for both experienced and new people to meet, present and discuss current and future DNSSEC deployments. For reference, the most recent session was held at the ICANN meeting in Dublin, Ireland on 21 October 2015. The presentations and transcripts are available at: https://meetings.icann.org/en/dublin54/schedule/wed-dnssec.
The DNSSEC Deployment Initiative and the Internet Society Deploy360 Programme, in cooperation with the ICANN Security and Stability Advisory Committee (SSAC), are planning a DNSSEC Workshop at the ICANN 55 meeting on 09 March 2016 in Marrakech, Morocco. The DNSSEC Workshop has been a part of ICANN meetings for several years and has provided a forum for both experienced and new people to meet, present and discuss current and future DNSSEC deployments. For reference, the most recent session was held at the ICANN meeting in Dublin, Ireland on 21 October 2015. The presentations and transcripts are available at: https://meetings.icann.org/en/dublin54/schedule/wed-dnssec.
At ICANN 55 we are particularly interested in live demonstrations of uses of DNSSEC or DANE. Examples might include:
* Email clients and servers using DNSSEC, OPENPGPKEY, or S/MIME for secure email.
* Tools for automating the generation of DNSSEC/DANE records.
* Services for monitoring or managing DNSSEC signing or validation.
* Tools or services for using DNSSEC/DANE along with other existing protocols and
services such as SSH, XMPP, SMTP, S/MIME or PGP/GPG.
* Innovative uses of APIs to do something new and different using DNSSEC/DANE.
* S/MIME and Microsoft Outlook integration with active directory.
Our interest is to provide current examples of the state of development and to show real-world examples of how DNSSEC and DANE related innovation can be used to increase the overall security of the Internet.
We are open to presentations and demonstrations related to any topic associated with DNSSEC and DANE.
If you are interested in participating, please send a brief (1-2 sentence) description of your proposed presentation to [email protected] by **Monday, 14 December 2015**
Examples of the types of topics we are seeking include:
1. DNSSEC activities in Africa
For this panel we are seeking participation from those who have been involved in DNSSEC deployment in Africa and also from those who have not deployed DNSSEC but who have a keen interest in the challenges and benefits of deployment. In particular, we will consider the following questions: Are you interested in reporting on DNSSEC validation of your ISPs? What can DNSSEC do for you? What doesn’t it do? What are the internal tradeoffs to implementing DNSSEC? What did you learn in your deployment of DNSSEC? We are interested in presentations from both people involved with the signing of domains and people involved with the deployment of DNSSEC-validating DNS resolvers.
2. Potential impacts of Root Key Rollover
Given many concerns about the need to do a Root Key Rollover, we would like to bring together a panel of people who can talk about what the potential impacts may be to ISPs, equipment providers and end users, and also what can be done to potentially mitigate those issues. In particular, we are seeking participation from vendors, ISPs, and the community that will be affected by distribution of new root keys. We would like to be able to offer suggestions out of this panel to the wider technical community. If you have a specific concern about the Root Key Rollover, or believe you have a method or solution to help address impacts, we would like to hear from you.
3. Implementing DNSSEC validation at Internet Service Providers (ISPs)
Internet Service Providers (ISPs) play a critical role by enabling DNSSEC validation for the caching DNS resolvers used by their customers. We have now seen massive rollouts of DNSSEC validation within large North American ISPs and at ISPs around the world. We are interested in presentations on topics such as:
* Can you describe your experiences with negative Trust Anchors and operational realities?
* What does an ISP need to do to prepare its network for implementing DNSSEC validation?
* How does an ISP need to prepare its support staff and technical staff for the rollout of DNSSEC validation?
* What measurements are available about the degree of DNSSEC validation currently deployed?
* What tools are available to help an ISP deploy DNSSEC validation?
* What are the practical server-sizing impacts of enabling DNSSEC validation on ISP DNS Resolvers (ex. cost, memory, CPU, bandwidth, technical support, etc.)?
4. The operational realities of running DNSSEC
Now that DNSSEC has become an operational norm for many registries, registrars, and ISPs, what have we learned about how we manage DNSSEC? What is the best practice around key rollovers? How often do you review your disaster recovery procedures? Is there operational familiarity within your customer support teams? What operational statistics have we gathered about DNSSEC? Are there experiences being documented in the form of best practices, or something similar, for transfer of signed zones?
5. DANE and DNSSEC application automation
For DNSSEC to reach massive deployment levels it is clear that a higher level of automation is required than is currently available. There also is strong interest for DANE usage within web transactions as well as for securing email and Voice-over-IP (VoIP). We are seeking presentations on topics such as:
* What tools, systems and services are available to help automate DNSSEC key management?
* Can you provide an analysis of current tools/services and identify gaps?
* Where are the best opportunities for automation within DNSSEC signing and validation processes?
* What are the costs and benefits of different approaches to automation?
* What are some of the new and innovative uses of DANE and other DNSSEC applications in new areas or industries?
* What tools and services are now available that can support DANE usage?
* How soon could DANE and other DNSSEC applications become a deployable reality?
* How can the industry use DANE and other DNSSEC applications as a mechanism for creating a more secure Internet?
We would be particularly interested in any live demonstrations of DNSSEC / DANE application automation and services. For example, a demonstration of the actual process of setting up a site with a certificate stored in a TLSA record that correctly validates would be welcome. Demonstrations of new tools that make the setup of DNSSEC or DANE more automated would also be welcome.
6. When unexpected DNSSEC events occur
What have we learned from some of the operational outages that we have seen over the past 18 months? Are there lessons that we can pass on to those just about to implement DNSSEC? How do you manage dissemination of information about the outage? What have you learned about communications planning? Do you have a route to ISPs and registrars? How do you liaise with your CERT community?
7. DNSSEC and DANE in the enterprise
Enterprises can play a critical role in both providing DNSSEC validation to their internal networks and also through signing of the domains owned by the enterprise. We are seeking presentations from enterprises that have implemented DNSSEC on validation and/or signing processes and can address questions such as:
* What are the benefits to enterprises of rolling out DNSSEC validation? And how do they do so?
* What are the challenges to deployment for these organizations and how could DANE and other DNSSEC applications address those challenges?
* How should an enterprise best prepare its IT staff and network to implement DNSSEC?
* What tools and systems are available to assist enterprises in the deployment of DNSSEC?
* How can the DANE protocol be used within an enterprise to bring a higher level of security to transactions using SSL/TLS certificates?
8. Hardware Security Modules (HSMs) use cases and innovation
We are interested in demonstrations of HSMs, presentations of HSM-related innovations and real world use cases of HSMs and key management.
In addition, we welcome suggestions for additional topics.
If you are interested in participating, please send a brief (1-2 sentence) description of your proposed presentation to [email protected] by **Monday, 14 December 2015**
We hope that you can join us.
Thank you,
Julie Hedlund
On behalf of the DNSSEC Workshop Program Committee:
Mark Elkins, DNS/ZACR
Cath Goulding, Nominet UK
Jean Robert Hountomey, AfricaCERT
Jacques Latour, .CA
Xiaodong Lee, CNNIC
Luciano Minuchin, NIC.AR
Russ Mundy, Parsons
Ondřej Surý, CZ.NIC
Yoshiro Yoneya, JPRS
Dan York, Internet Society
Video And Slides Available for ICANN 54 DNSSEC Workshop
Posted by Dan York in DNSSEC, ICANN DNSSEC Workshops on October 30, 2015
 The video and slides are now available from the 6-hour DNSSEC Workshop at ICANN 54 in Dublin this month. You can see the agenda and download all the slides at:
The video and slides are now available from the 6-hour DNSSEC Workshop at ICANN 54 in Dublin this month. You can see the agenda and download all the slides at:
https://meetings.icann.org/en/dublin54/schedule/wed-dnssec
The session was recorded in two video segments due to the lunch break:
Both videos are embedded below the agenda for those wanting to play them right here while seeing the agenda.
The agenda for the session was:
0900-0915 – DNSSEC Workshop Introduction, Program, Deployment Around the World – Counts, Counts, Counts
|
0915-1045 – Panel Discussion: DNSSEC Activities in the European Region
|
| 1045-1100 – Break |
1100-1215 – Panel Discussion: DNSSEC On The Edge
|
1215-1230 – Great DNS/DNSSEC Quiz
|
| 1230-1315 – Lunch Break |
1315-1430 – Demonstrations and Presentations: DNSSEC and Applications
|
1430-1500 – Presentation: Stimulating DNSSEC Validation for .NL
|
1500-1515 – Presentation: DNSSEC – How Can I Help?
|
The video for the morning session is:
The video for the afternoon session is:
Thank you to everyone involved session – we’ll look forward to doing it again at ICANN 55 in Marakech!
WATCH FOR THE ICANN 55 DNSSEC WORKSHOP CALL FOR PRESENTATIONS – COMING SOON!
And if you want to get started with DNSSEC, check out the Deploy360 Start Here page as a place to begin.
ICANN 54 – DNSSEC For Everybody: A Beginner’s Guide – Video and Slides Available
Posted by Dan York in ICANN DNSSEC Workshops on October 30, 2015
 Want to see the “skit” that explains DNS and DNSSEC? At the recently completed ICANN 54 meeting in Dublin, we recorded the skit and the other introductory slides and questions in a video available on the Deploy360 YouTube channel. The basic page for the DNSSEC For Everybody session that includes the slides and handout can be found at:
Want to see the “skit” that explains DNS and DNSSEC? At the recently completed ICANN 54 meeting in Dublin, we recorded the skit and the other introductory slides and questions in a video available on the Deploy360 YouTube channel. The basic page for the DNSSEC For Everybody session that includes the slides and handout can be found at:
https://meetings.icann.org/en/dublin54/schedule/mon-dnssec-everybody
The video recording is available online and embedded here:
Thank you to everyone involved in the skit and session – we’ll look forward to doing it again at ICANN 55 in Marakech!
And if you want to get started with DNSSEC, check out the Deploy360 Start Here page as a place to begin.
Call for Participation – DNSSEC Workshop at ICANN 54 in Dublin, Ireland
Posted by Dan York in DNSSEC, ICANN DNSSEC Workshops on July 31, 2015
 The DNSSEC Deployment Initiative and the Internet Society Deploy360 Programme, in cooperation with the ICANN Security and Stability Advisory Committee (SSAC), are planning a DNSSEC Workshop at the ICANN 54 meeting on 21 October in Dublin, Ireland. The DNSSEC Workshop has been a part of ICANN meetings for several years and has provided a forum for both experienced and new people to meet, present and discuss current and future DNSSEC deployments. For reference, the most recent session was held at the ICANN meeting in Buenos Aires, Argentina on 24 June 2015. The presentations and transcripts are available at: https://buenosaires53.icann.org/en/schedule/wed-dnssec.
The DNSSEC Deployment Initiative and the Internet Society Deploy360 Programme, in cooperation with the ICANN Security and Stability Advisory Committee (SSAC), are planning a DNSSEC Workshop at the ICANN 54 meeting on 21 October in Dublin, Ireland. The DNSSEC Workshop has been a part of ICANN meetings for several years and has provided a forum for both experienced and new people to meet, present and discuss current and future DNSSEC deployments. For reference, the most recent session was held at the ICANN meeting in Buenos Aires, Argentina on 24 June 2015. The presentations and transcripts are available at: https://buenosaires53.icann.org/en/schedule/wed-dnssec.
At ICANN 54 we are particularly interested in live demonstrations of uses of DNSSEC or DANE. Examples might include:
- Email clients and servers using DNSSEC, OPENPGPKEY, or S/MIME for secure email.
- Tools for automating the generation of DNSSEC/DANE records.
- Services for monitoring or managing DNSSEC signing or validation.
- Tools or services for using DNSSEC/DANE along with other existing protocols and services such as SSH, XMPP, SMTP, S/MIME or PGP/GPG.
- Innovative uses of APIs to do something new and different using DNSSEC/DANE.
- S/MIME and Microsoft Outlook integration with active directory.
Our interest is to provide current examples of the state of development and to show real-world examples of how DNSSEC and DANE related innovation can be used to increase the overall security of the Internet.
We are open to presentations and demonstrations related to any topic associated with DNSSEC and DANE. Examples of the types of topics we are seeking include:
1. DNSSEC activities in Europe
For this panel we are seeking participation from those who have been involved in DNSSEC deployment in Europe and also from those who have not deployed DNSSEC but who have a keen interest in the challenges and benefits of deployment. In particular, we will consider the following questions: Are you interested in reporting on DNSSEC validation of your ISPs? What can DNSSEC do for you? What doesn’t it do? What are the internal tradeoffs to implementing DNSSEC? What did you learn in your deployment of DNSSEC? We are interested in presentations from both people involved with the signing of domains and people involved with the deployment of DNSSEC-validating DNS resolvers.
2. Potential impacts of Root Key Rollover
Given many concerns about the need to do a Root Key Rollover, we would like to bring together a panel of people who can talk about what the potential impacts may be to ISPs, equipment providers and end users, and also what can be done to potentially mitigate those issues. In particular, we are seeking participation from vendors, ISPs, and the community that will be affected by distribution of new root keys. We would like to be able to offer suggestions out of this panel to the wider technical community. If you have a specific concern about the Root Key Rollover, or believe you have a method or solution to help address impacts, we would like to hear from you.
3. Implementing DNSSEC validation at Internet Service Providers (ISPs)
Internet Service Providers (ISPs) play a critical role by enabling DNSSEC validation for the caching DNS resolvers used by their customers. We have now seen massive rollouts of DNSSEC validation within large North American ISPs and at ISPs around the world. We are interested in presentations on topics such as:
- Can you describe your experiences with negative Trust Anchors and operational realities?
- What does an ISP need to do to prepare its network for implementing DNSSEC validation?
- How does an ISP need to prepare its support staff and technical staff for the rollout of DNSSEC validation?
- What measurements are available about the degree of DNSSEC validation currently deployed?
- What tools are available to help an ISP deploy DNSSEC validation?
- What are the practical server-sizing impacts of enabling DNSSEC validation on ISP DNS Resolvers (ex. cost, memory, CPU, bandwidth, technical support, etc.)?
4. The operational realities of running DNSSEC
Now that DNSSEC has become an operational norm for many registries, registrars, and ISPs, what have we learned about how we manage DNSSEC? What is the best practice around key rollovers? How often do you review your disaster recovery procedures? Is there operational familiarity within your customer support teams? What operational statistics have we gathered about DNSSEC? Are there experiences being documented in the form of best practices, or something similar, for transfer of signed zones?
5. DANE and DNSSEC application automation
For DNSSEC to reach massive deployment levels it is clear that a higher level of automation is required than is currently available. There also is strong interest for DANE usage within web transactions as well as for securing email and Voice-over-IP (VoIP). We are seeking presentations on topics such as:
- What tools, systems and services are available to help automate DNSSEC key management?
- Can you provide an analysis of current tools/services and identify gaps?
- Where are the best opportunities for automation within DNSSEC signing and validation processes?
- What are the costs and benefits of different approaches to automation?
- What are some of the new and innovative uses of DANE and other DNSSEC applications in new areas or industries?
- What tools and services are now available that can support DANE usage?
- How soon could DANE and other DNSSEC applications become a deployable reality?
- How can the industry use DANE and other DNSSEC applications as a mechanism for creating a more secure Internet?
We would be particularly interested in any live demonstrations of DNSSEC / DANE application automation and services. For example, a demonstration of the actual process of setting up a site with a certificate stored in a TLSA record that correctly validates would be welcome. Demonstrations of new tools that make the setup of DNSSEC or DANE more automated would also be welcome.
6. When unexpected DNSSEC events occur
What have we learned from some of the operational outages that we have seen over the past 18 months? Are there lessons that we can pass on to those just about to implement DNSSEC? How do you manage dissemination of information about the outage? What have you learned about communications planning? Do you have a route to ISPs and registrars? How do you liaise with your CERT community?
7. DNSSEC and DANE in the enterprise
Enterprises can play a critical role in both providing DNSSEC validation to their internal networks and also through signing of the domains owned by the enterprise. We are seeking presentations from enterprises that have implemented DNSSEC on validation and/or signing processes and can address questions such as:
- What are the benefits to enterprises of rolling out DNSSEC validation? And how do they do so?
- What are the challenges to deployment for these organizations and how could DANE and other DNSSEC applications address those challenges?
- How should an enterprise best prepare its IT staff and network to implement DNSSEC?
- What tools and systems are available to assist enterprises in the deployment of DNSSEC?
- How can the DANE protocol be used within an enterprise to bring a higher level of security to transactions using SSL/TLS certificates?
8. Hardware Security Modules (HSMs) use cases and innovation
We are interested in demonstrations of HSMs, presentations of HSM-related innovations and real world use cases of HSMs and key management.
In addition, we welcome suggestions for additional topics.
If you are interested in participating, please send a brief (1-2 sentence) description of your proposed presentation to [email protected] by **Monday, 17 August 2015**
We hope that you can join us.
On behalf of the DNSSEC Workshop Program Committee:
Mark Elkins, DNS/ZACR
Cath Goulding, Nominet UK
Julie Hedlund, ICANN
Jean Robert Hountomey, AfricaCERT
Jacques Latour, .CA
Xiaodong Lee, CNNIC
Luciano Minuchin, NIC.AR
Russ Mundy, Parsons
Ondřej Surý, CZ.NIC
Yoshiro Yoneya, JPRS
Dan York, Internet Society
Agenda Available for ICANN 53 DNSSEC Workshop on 24 June 2015 in Buenos Aires
Posted by Dan York in DNSSEC, ICANN DNSSEC Workshops on June 16, 2015
 It’s time to talk DNSSEC and DANE in Latin America! The DNSSEC Workshop at ICANN 53 in Buenos Aires will take place on Wednesday, 24 June 2015, from 9:00 to 15:15 ART. NOTE THE LATER START TIME! Previously the workshops started at 8:30am but this time our start is 9:00.
It’s time to talk DNSSEC and DANE in Latin America! The DNSSEC Workshop at ICANN 53 in Buenos Aires will take place on Wednesday, 24 June 2015, from 9:00 to 15:15 ART. NOTE THE LATER START TIME! Previously the workshops started at 8:30am but this time our start is 9:00.
Remote participation information, slides, the agenda and more info can be found at:
https://buenosaires53.icann.org/en/schedule/wed-dnssec
The sessions will be recorded if you would like to listen to them later. Slides will be posted as the date gets closer.
The current agenda includes (all times are Argentina Time (ART) which is UTC-3):
0900-0915 – DNSSEC Workshop Introduction, Program, Deployment Around the World – Counts, Counts, Counts
|
0915-1030 – Panel Discussion: DNSSEC Activities in the Latin American Region
|
1030-1100 – Presentation: Update on DNSSEC KSK Root Key Rollover
|
| 1100-1115 – Break |
1115-1215 – Panel Discussion: DNSSEC Automation
|
1215-1230 – Great DNS/DNSSEC Quiz
|
| 1230-1330 – Lunch Break |
1330-1445 – Demonstrations and Presentations: DANE and Applications
|
1445-1500 – Presentation: Deploying New DNSSEC Algorithms
|
1500-1515 – Presentation: DNSSEC – How Can I Help?
|
We look forward to seeing you there!
Call for Participation – ICANN 53 DNSSEC Workshop in Buenos Aires, Argentina, 24 June 2015
Posted by Dan York in DNSSEC, ICANN DNSSEC Workshops, Meetings and Workshops on March 11, 2015
 Do you have a great story to share about your DNSSEC implementation? Do you have a new tool or service that makes DNSSEC or DANE easier to use or more automated? Would you like to demo your new tool or service? Do you have a case study you’d like to share?
Do you have a great story to share about your DNSSEC implementation? Do you have a new tool or service that makes DNSSEC or DANE easier to use or more automated? Would you like to demo your new tool or service? Do you have a case study you’d like to share?
We’re starting the call for participation for the ICANN 53 DNSSEC Workshop on Wednesday, June 24, 2015, at ICANN 53 in Buenos Aires, Argentina and we’d love to hear your ideas about what you would like to present. If you will be at ICANN 53, or can get there, please do consider submitting a proposal. You just need to send a sentence or two about your idea to:
by Wednesday, 01 April 2015.
If you are looking for ideas for topics, we’ve listed a good number of sessions we’d like to hear about in the full Call for Participation below. Consider these as starting points… we’re also interested in any other ideas you may have. We typically have about 100 people participating from across the industry and the Workshops provide a great way to share information with others – and to get input/feedback on ideas and services you may have.
Please consider joining us!
Call for Participation — ICANN DNSSEC Workshop at ICANN 53 in Buenos Aires, Argentina
The DNSSEC Deployment Initiative and the Internet Society Deploy360 Programme, in cooperation with the ICANN Security and Stability Advisory Committee (SSAC), are planning a DNSSEC Workshop at the ICANN 53 meeting on 24 June 2015 in Buenos Aires, Argentina. The DNSSEC Workshop has been a part of ICANN meetings for several years and has provided a forum for both experienced and new people to meet, present and discuss current and future DNSSEC deployments. For reference, the most recent session was held at the ICANN meeting in Singapore on 11 February 2015. The presentations and transcripts are available at: http://singapore52.icann.org/en/schedule/wed-dnssec.
At ICANN 53 we are particularly interested in live demonstrations of uses of DNSSEC or DANE. Examples might include:
- Email clients and servers using DNSSEC/DANE for secure email.
- Tools for automating the generation of DNSSEC/DANE records.
- Services for monitoring or managing DNSSEC signing or validation.
- Tools or services for using DNSSEC/DANE along with other existing protocols and services such as SSH, FTP or PGP/GPG.
- Innovative uses of APIs to do something new and different using DNSSEC/DANE.
Our interest is to provide current examples of the state of development and to show real-world examples of how DNSSEC and DANE can be used to increase the overall security of the Internet.
We are open to presentations and demonstrations related to any topic associated with DNSSEC and DANE. Examples of the types of topics we are seeking include:
1. DNSSEC activities in Latin America
For this panel we are seeking participation from those who have been involved in DNSSEC deployment in Latin America and also from those who have not deployed DNSSEC but who have a keen interest in the challenges and benefits of deployment. In particular, we will consider the following questions: What can DNSSEC do for you? What doesn’t it do? What are the internal tradeoffs to implementing DNSSEC? What did you learn in your deployment of DNSSEC? We are interested in presentations from both people involved with the signing of domains and people involved with the deployment of DNSSEC-validating DNS resolvers.
2. Potential impacts of Root Key Rollover
Given many concerns about the need to do a Root Key Rollover, we would like to bring together a panel of people who can talk about what the potential impacts may be to ISPs, equipment providers and end users, and also what can be done to potentially mitigate those issues. In particular, we are seeking participation from vendors, ISPs, and the community that will be affected by distribution of new root keys. We would like to be able to offer suggestions out of this panel to the wider technical community. If you have a specific concern about the Root Key Rollover, or believe you have a method or solution to help address impacts, we would like to hear from you.
3. New gTLD registries and administrators implementing DNSSEC
With the launch of the new gTLDs, we are interested in hearing from registries and operators of new gTLDs about what systems and processes they have implemented to support DNSSEC. As more gTLDs are launched, is there DNSSEC-related information that can be shared to help those launches go easier?
4. Guidance for Registrars in supporting DNSSEC
The 2013 Registrar Accreditation Agreement (RAA) for registrars and resellers requires them to support DNSSEC from January 1, 2014. We are seeking presentations discussing:
- What are the specific technical requirements of the RAA and how can registrars meet those requirements?
- What tools and systems are available for registrars that include DNSSEC support?
- What information do registrars need to provide to resellers and ultimately customers?
We are particularly interested in hearing from registrars who have signed the 2013 RAA and have either already implemented DNSSEC support or have a plan for doing so.
5
Internet Service Providers (ISPs) play a critical role by enabling DNSSEC validation for the caching DNS resolvers used by their customers. We have now seen massive rollouts of DNSSEC validation within large North American ISPs and at ISPs around the world. We are interested in presentations on topics such as:
- What does an ISP need to do to prepare its network for implementing DNSSEC validation?
- How does an ISP need to prepare its support staff and technical staff for the rollout of DNSSEC validation?
- What measurements are available about the degree of DNSSEC validation currently deployed?
- What tools are available to help an ISP deploy DNSSEC validation?
- What are the practical server-sizing impacts of enabling DNSSEC validation on ISP DNS Resolvers (ex. cost, memory, CPU, bandwidth, technical support, etc.)?
6. The operational realities of running DNSSEC
Now that DNSSEC has become an operational norm for many registries, registrars, and ISPs, what have we learned about how we manage DNSSEC? What is the best practice around key rollovers? How often do you review your disaster recovery procedures? Is there operational familiarity within your customer support teams? What operational statistics have we gathered about DNSSEC? Are there experiences being documented in the form of best practices, or something similar, for transfer of signed zones?
7. DNSSEC automation
For DNSSEC to reach massive deployment levels it is clear that a higher level of automation is required than is currently available. Topics for which we would like to see presentations include:
- What tools, systems and services are available to help automate DNSSEC key management?
- Can you provide an analysis of current tools/services and identify gaps?
- Where are the best opportunities for automation within DNSSEC signing and validation processes?
- What are the costs and benefits of different approaches to automation?
8. When unexpected DNSSEC events occur
What have we learned from some of the operational outages that we have seen over the past 18 months? Are there lessons that we can pass on to those just about to implement DNSSEC? How do you manage dissemination of information about the outage? What have you learned about communications planning? Do you have a route to ISPs and registrars? How do you liaise with your CERT community?
9. DANE and DNSSEC applications
There is strong interest for DANE usage within web transactions as well as for securing email and Voice-over-IP (VoIP). We are seeking presentations on topics such as:
- What are some of the new and innovative uses of DANE and other DNSSEC applications in new areas or industries?
- What tools and services are now available that can support DANE usage?
- How soon could DANE and other DNSSEC applications become a deployable reality?
- How can the industry use DANE and other DNSSEC applications as a mechanism for creating a more secure Internet?
We would be particularly interested in any live demonstrations of DNSSEC / DANE applications and services. For example, a demonstration of the actual process of setting up a site with a certificate stored in a TLSA record that correctly validates would be welcome. Demonstrations of new tools that make the setup of DNSSEC or DANE more automated would also be welcome.
10. DNSSEC and DANE in the enterprise
Enterprises can play a critical role in both providing DNSSEC validation to their internal networks and also through signing of the domains owned by the enterprise. We are seeking presentations from enterprises that have implemented DNSSEC on validation and/or signing processes and can address questions such as:
- What are the benefits to enterprises of rolling out DNSSEC validation? And how do they do so?
- What are the challenges to deployment for these organizations and how could DANE and other DNSSEC applications address those challenges?
- How should an enterprise best prepare its IT staff and network to implement DNSSEC?
- What tools and systems are available to assist enterprises in the deployment of DNSSEC?
- How can the DANE protocol be used within an enterprise to bring a higher level of security to transactions using SSL/TLS certificates?
11. Hardware Security Modules (HSMs) use cases and innovation
We are interested in demonstrations of HSMs, presentations of HSM-related innovations and real world use cases of HSMs and key management.
In addition, we welcome suggestions for additional topics.
If you are interested in participating, please send a brief (1-2 sentence) description of your proposed presentation to [email protected] by Wednesday, 01 April 2015
We hope that you can join us.
Thank you,
Julie Hedlund
On behalf of the DNSSEC Workshop Program Committee:
Mark Elkins, DNS/ZACR
Cath Goulding, Nominet UK
Jean Robert Hountomey, AfricaCERT
Jacques Latour, .CA
Xiaodong Lee, CNNIC
Luciano Minuchin, NIC.AR
Russ Mundy, Parsons
Ondřej Surý, CZ.NIC
Yoshiro Yoneya, JPRS
Dan York, Internet Society


Recent Comments